Secure Every AI Interaction Across Endpoints
Real-Time Enforcement and Governance (AI-EDR) for AI Agents, MCP Servers and Coding Assistants
AI Agents Introduce Security Risks EDR Doesn't Address
Cursor, Claude Code and other agents now act directly on systems and data. They can legitimately:
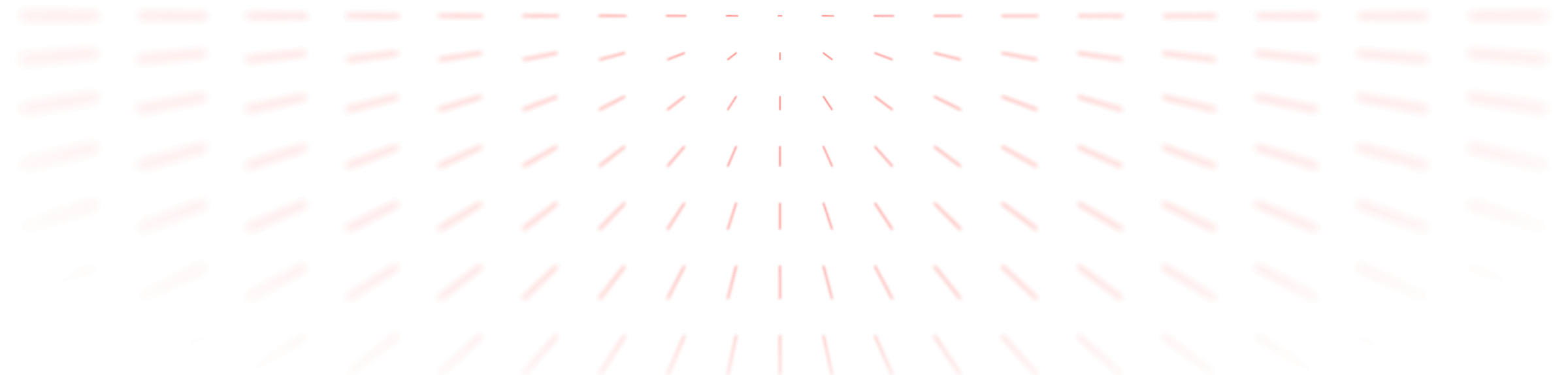
Traditional endpoint controls were never designed for agent behavior. Without controls at the endpoint, security teams cannot govern agent actions, MCPs, skills, data access, or credential use.
Let Your Org Run Fast With AI, but Mitigate the Risks


Approval Fatigue
Employees face dozens of agent actions per task, rendering manual approvals impractical and increasing risk.
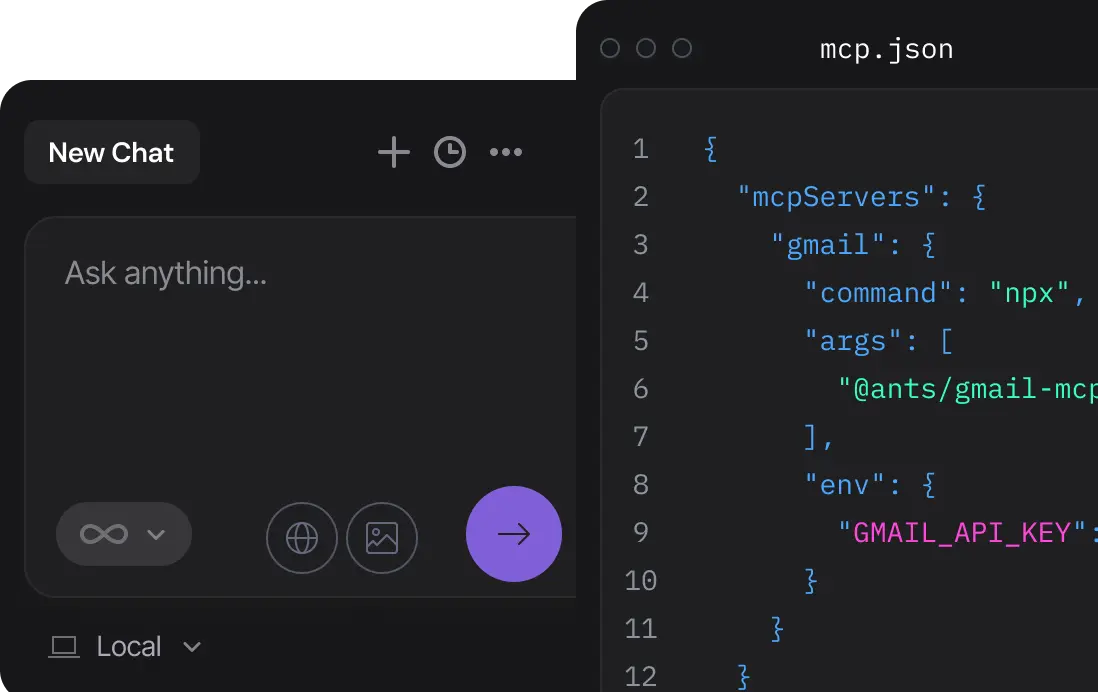
Credential Sprawl
Secrets live inside developer environments in files, environment variables and ad-hoc configurations - unprotected and unmanaged.
Untrusted Agent Workloads
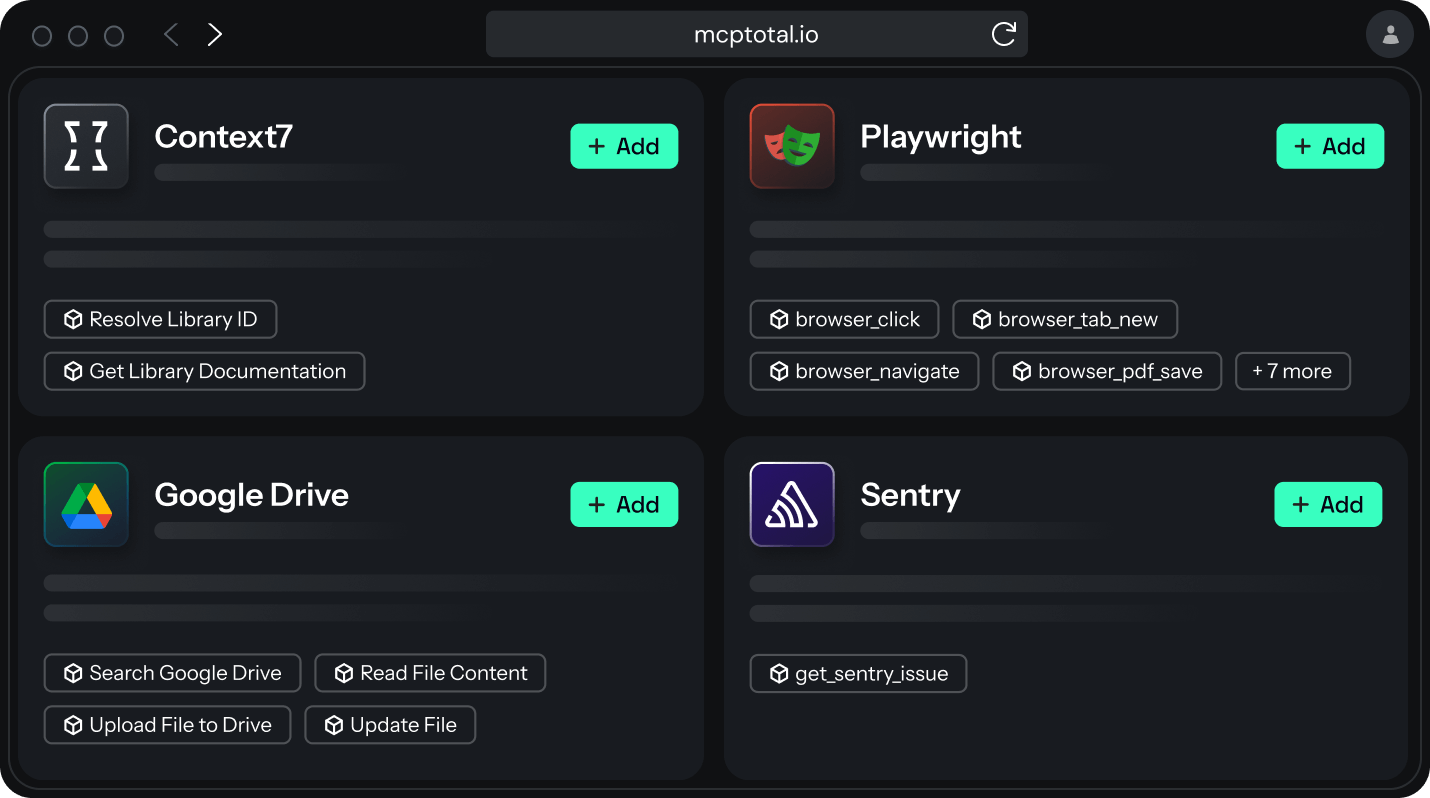
MCP servers, plugins and skills can be added freely, operating with privileged access to sensitive systems and data.
Lack of Visibility
Security teams cannot see which agents are running, what tools or MCP servers they invoke, or how data moves during agent execution.
No Runtime Enforcement
Unsafe agent actions cannot be constrained or blocked as they occur.
New AI Attack Surface
Prompt injection, malicious skills, MCP servers and MCP-specific attacks enable data breaches.
The MCPTotal Control Stack
MCPTotal restores control over agent execution on the endpoints through three integrated layers, built for how agents and MCP actually operate.
Shadow AI & Agent Discovery

Gain instant visibility into agentic activity across all workstations.
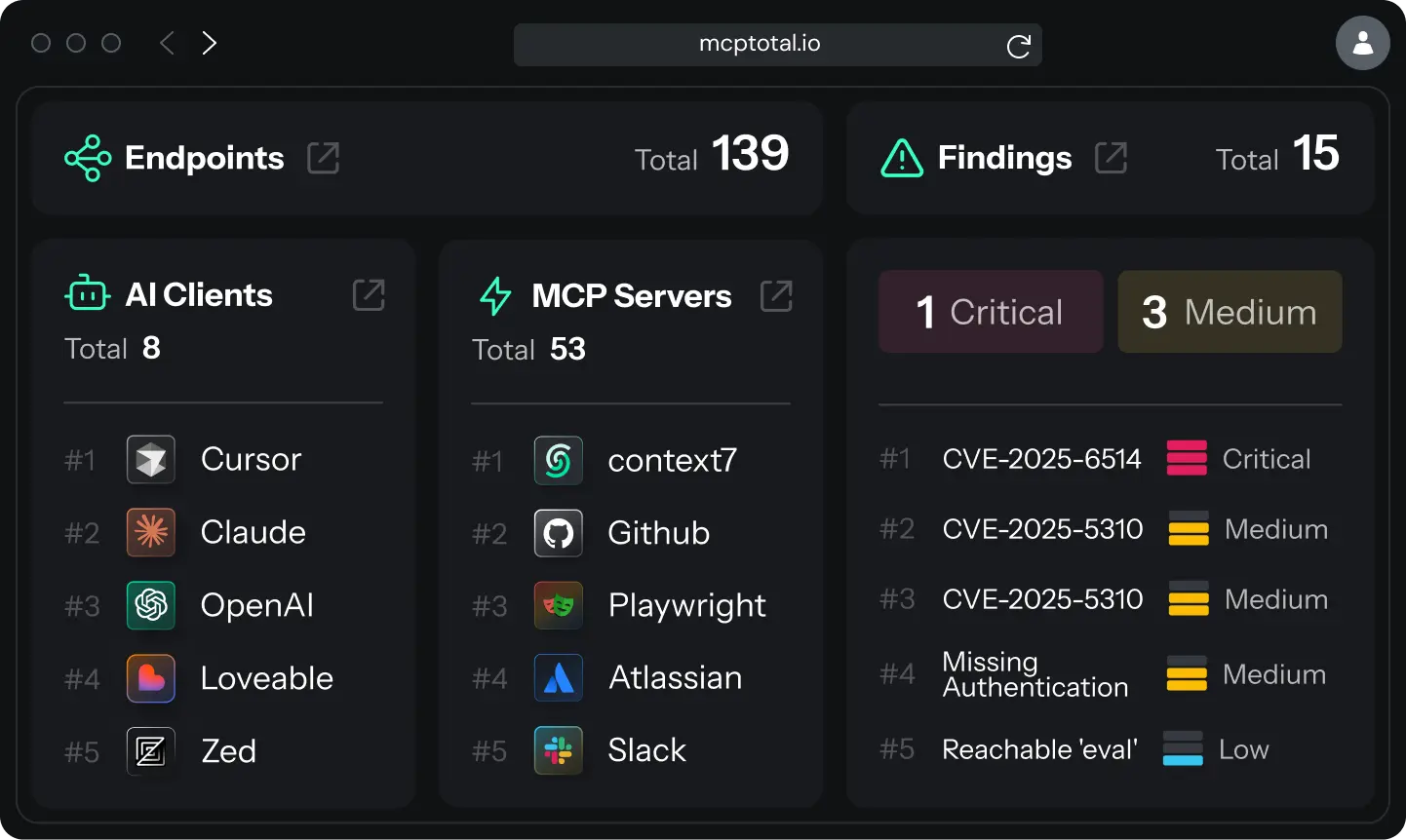
AI Inventory
Discover every installed agent, skills, plugins and MCP server
Exposure Analysis
Identify exposed configs and hardcoded secrets instantly
Risk Assessment
Report on risk and security posture for all agentic activity

Runtime Enforcement

Control AI agent behavior in real-time across endpoints and IDEs.
MCPTotal provides an OS-native security agent to monitor and enforce controls at execution time.
Cross Platform
Deploy agents anywhere (Win, Mac, Linux) with flexible distribution methods
Threats Prevention
Secure your environment by auto-blocking rogue MCPs and malicious skills
MCP Gateway
Prevent prompt injections with automatic MCP traffic interception
Secure MCP Cloud

Move MCP servers and credentials out of unmanaged local environments and into a secure, isolated cloud.
Sandboxing
Secure your MCP operations within isolated, sandboxed environments
Token Vault
Protect sensitive credentials by storing tokens in a centralized token vault
Supply Chain Security
Eliminate supply-chain threats using our verified, pre-scanned MCP catalog
From Control to Governance
Centralized policy, identity and audit across all agentic activity. The governance plane defines what agents are allowed to do — and enforces it at runtime.
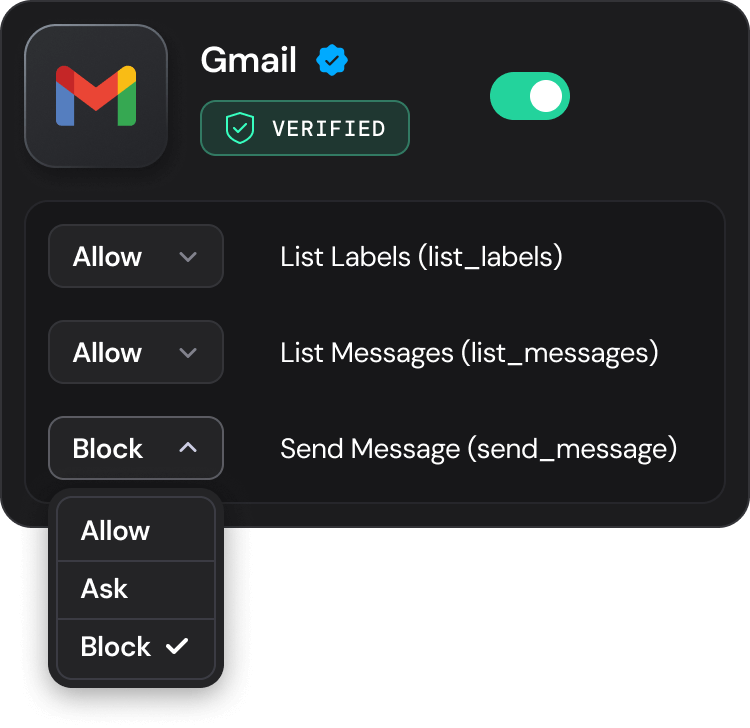
Policies
Control various activity operations, tools, MCP servers, authentication methods and many more
Safe Run
Automate approvals of prompts, command shells and tools based on security risk
Enterprise-ready
Integrate with SSO/SCIM, SIEM and enterprise compliance requirements
Learn how we can quickly discover shadow AI in your endpoints
Frequently Asked Questions
Everything you need to know about MCP security and our platform

